Taking away the complexity of SSL monitoring
The world of SSL/TLS has become very complex. We can take away that complexity for you and present you with an easy-to-use monitoring solution for your SSL certificates.
We'll monitor your website's certificate expiration dates and send you a notification when they're about to expire.
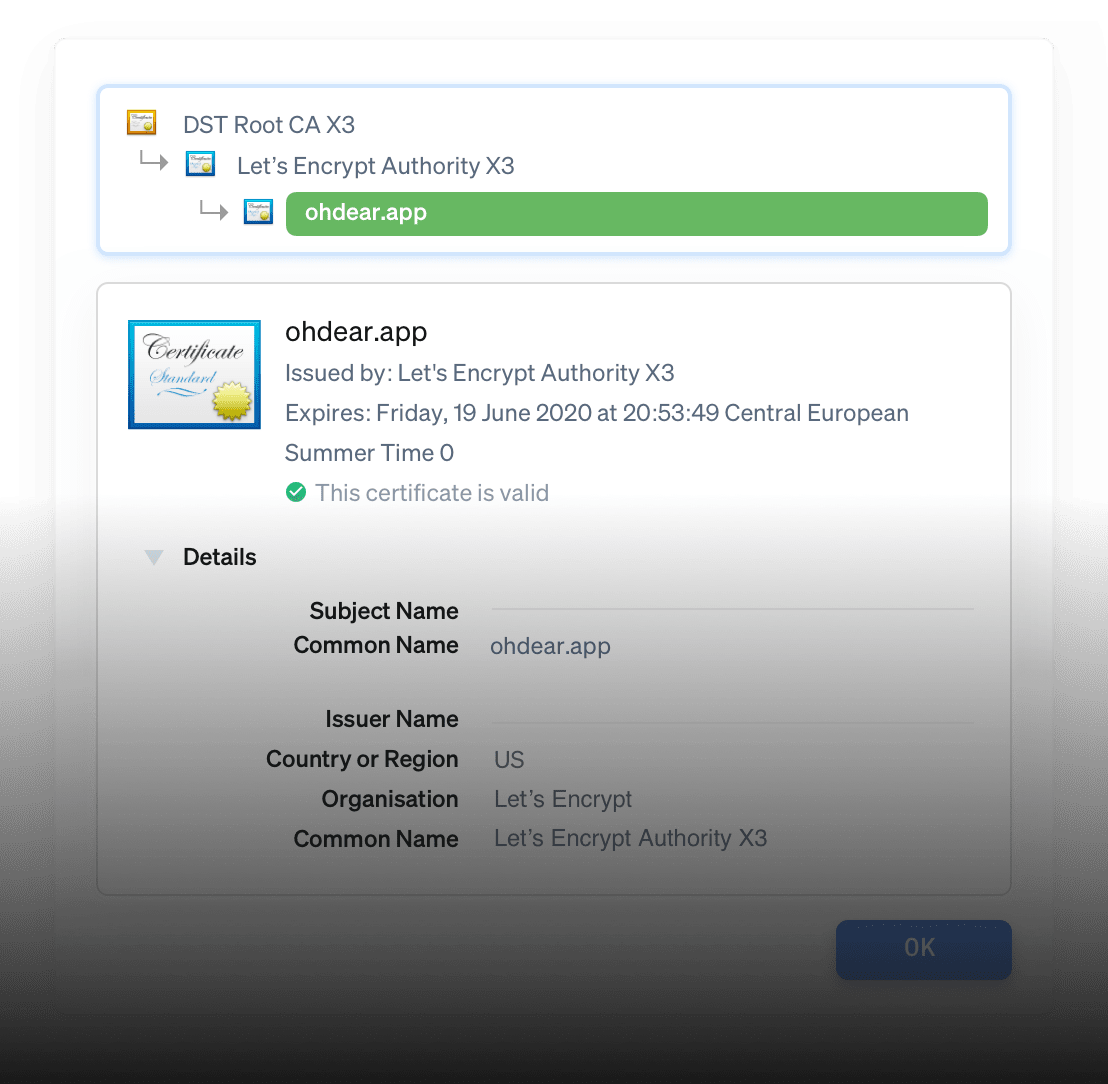
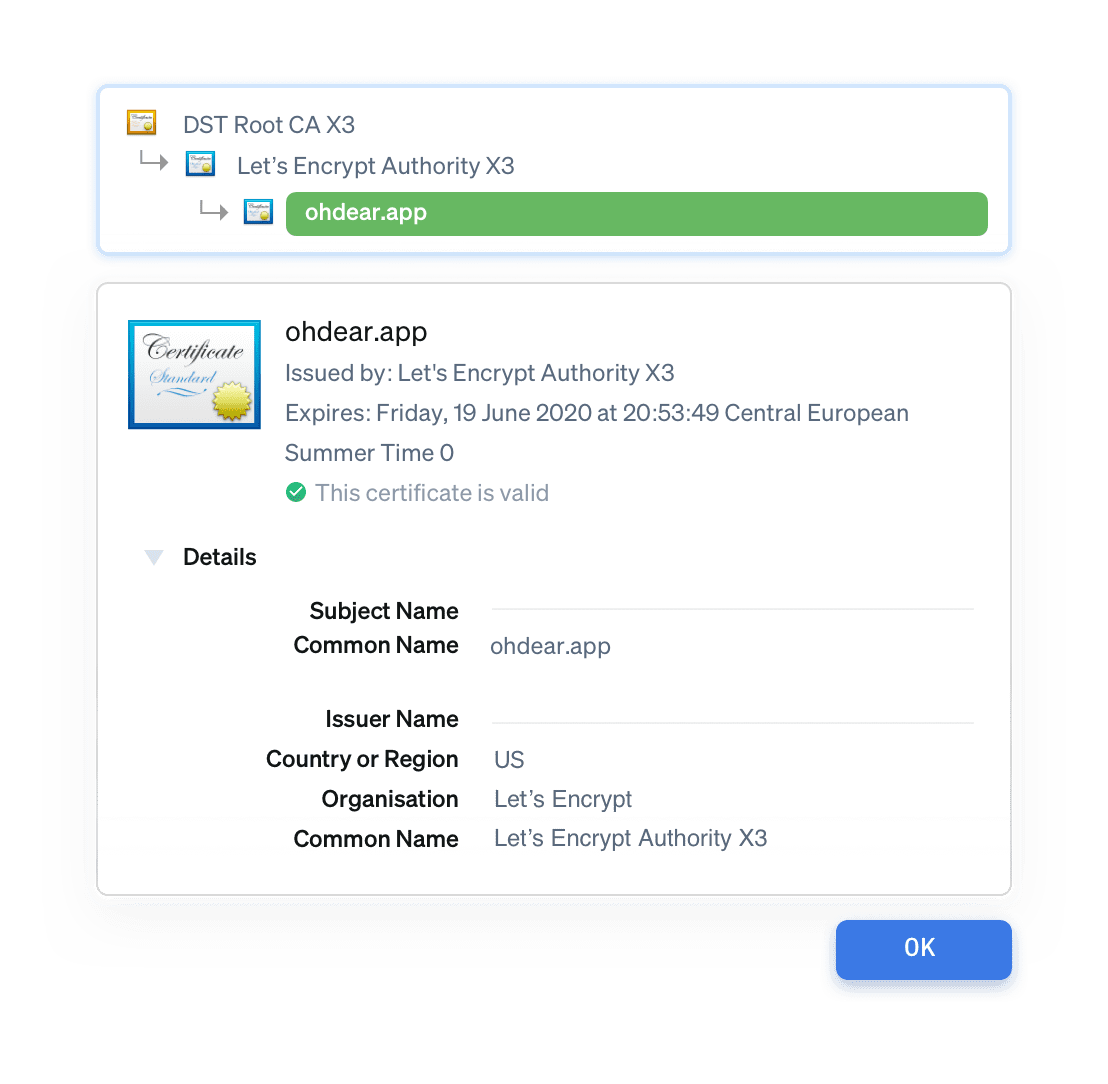
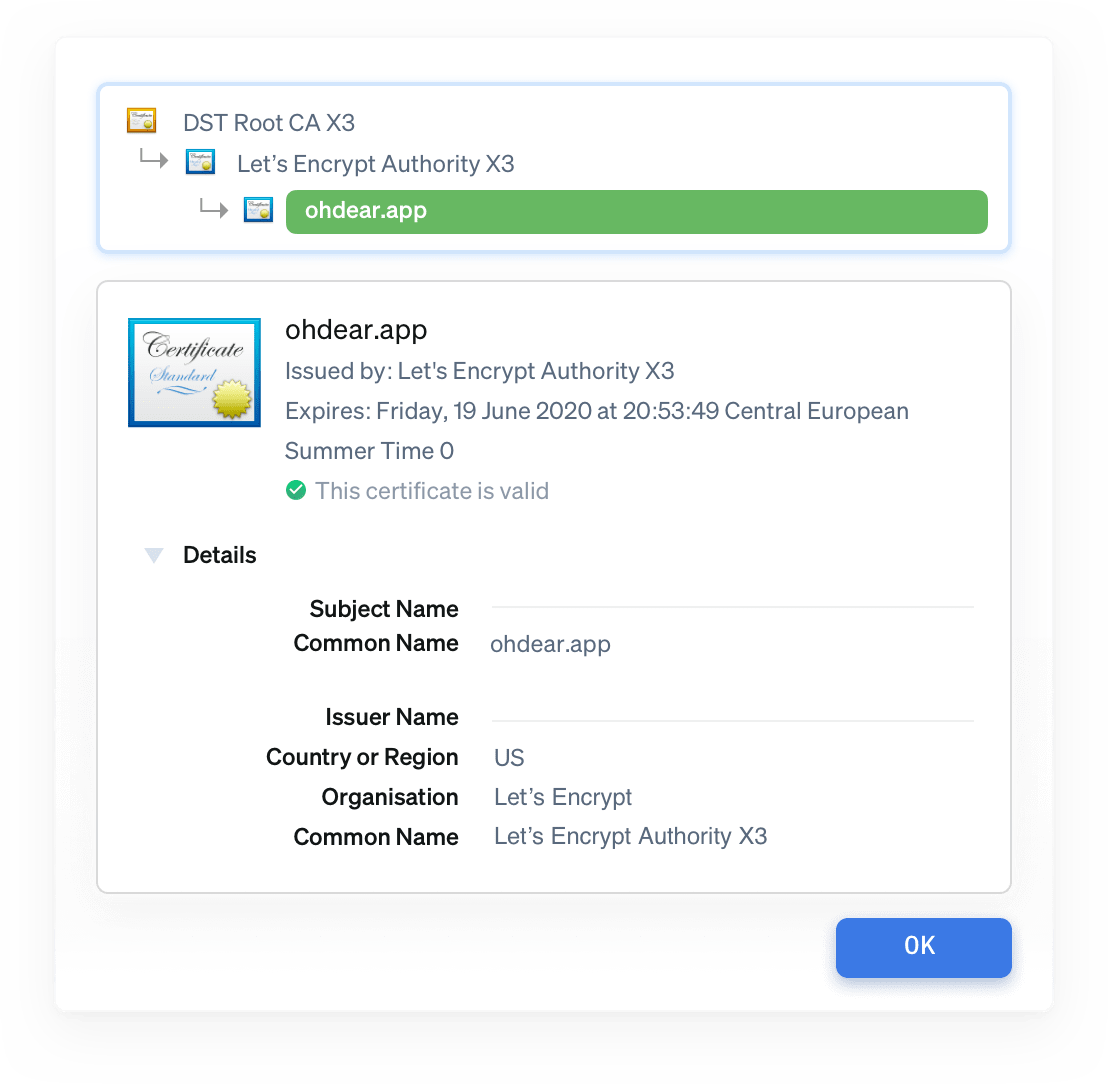
- Certificates form a chain of trust. We don't only monitor your domain (leaf) certificate, but every intermediate too.
- Other monitoring tools often only check the domain certificate.
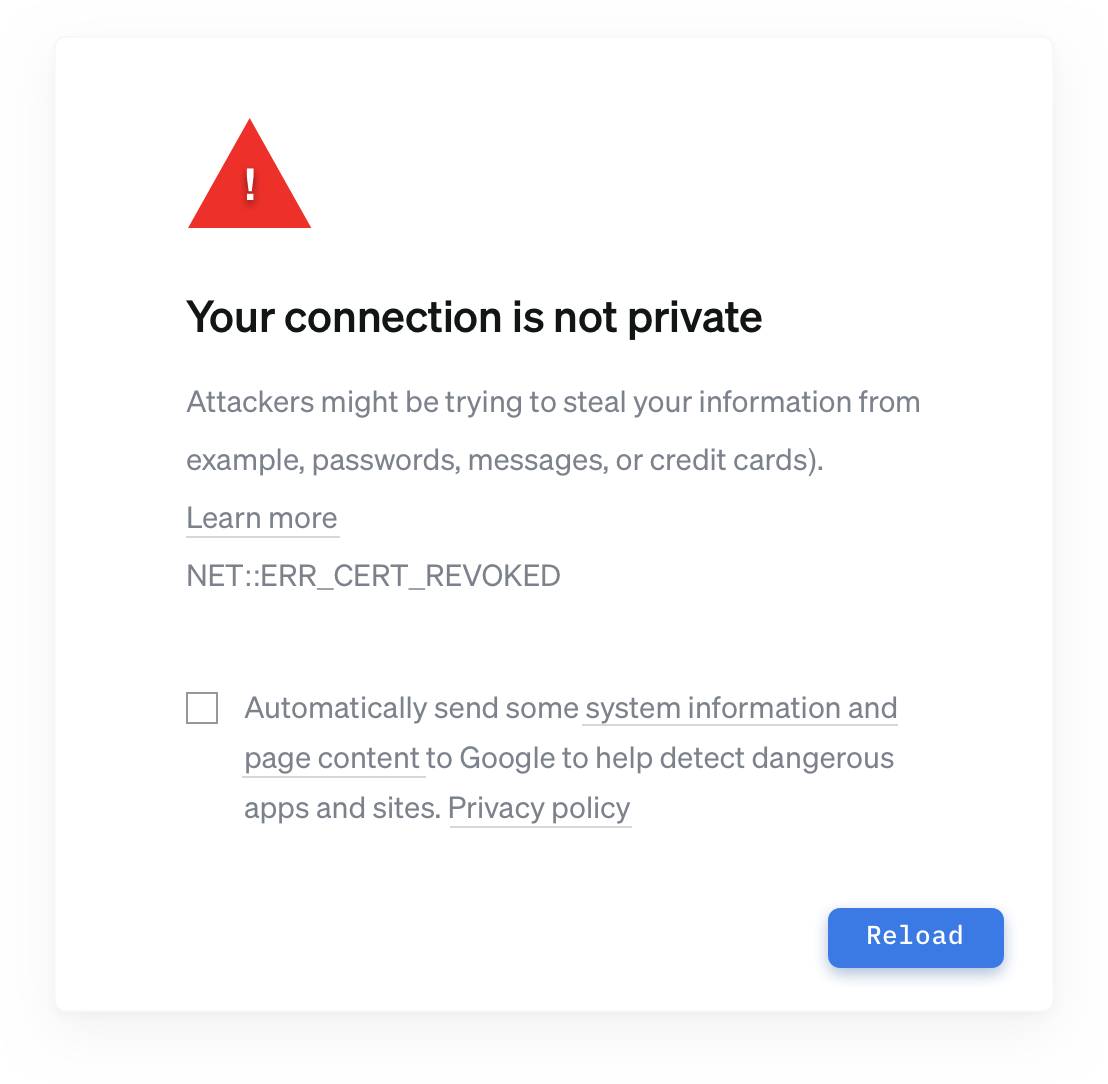
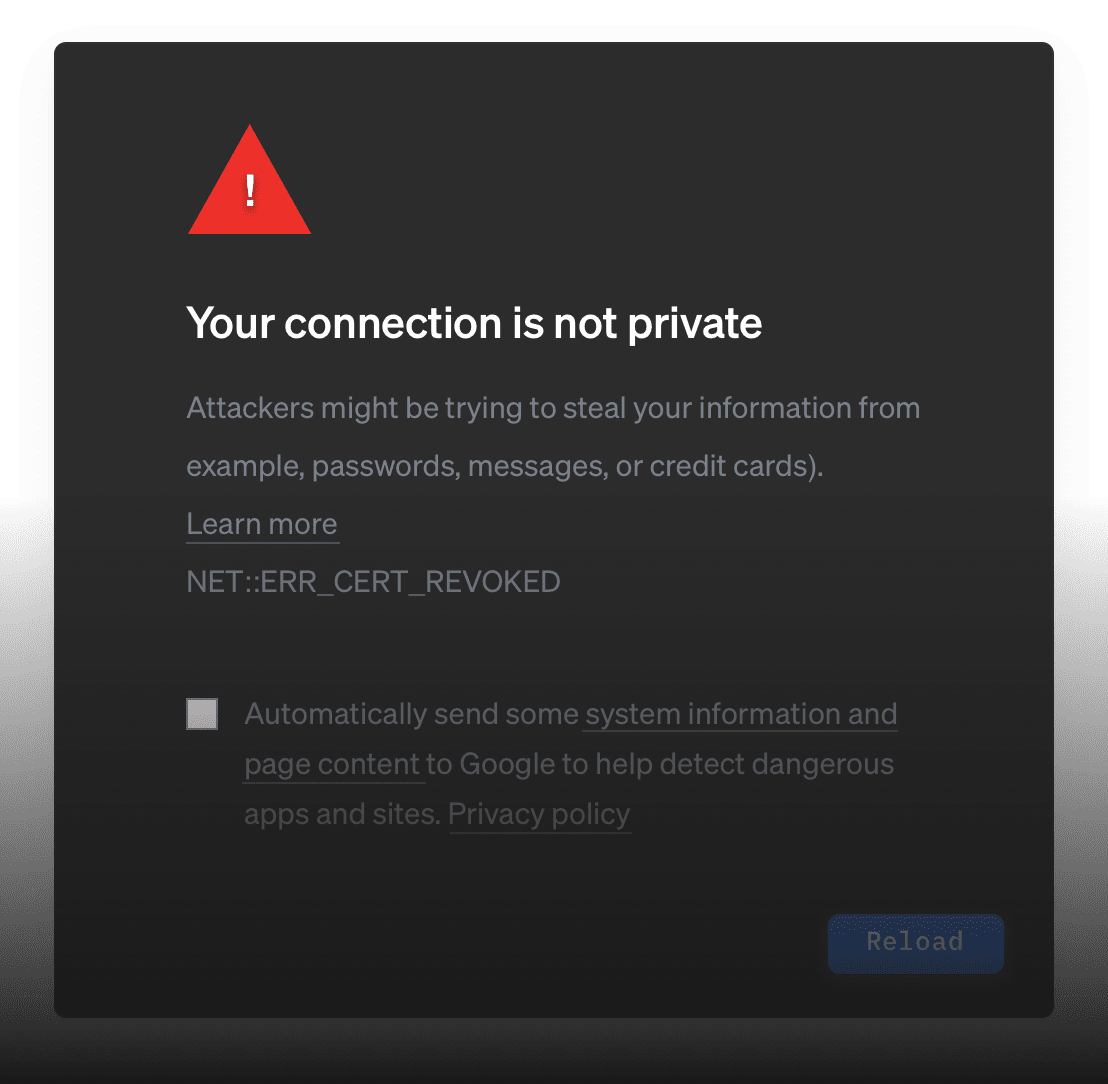
Your visitors will get an error message
If you're using old security algorithms, some browsers will block access to your site. We detect those old ciphers and report them to you.
Error messages like this negatively affect your brand image (and ultimately, your bottom line) as they make your website feel inaccessible and untrustworthy. Keeping track of your certificates avoids these unpleasant surprises.
| Component | Value |
|---|---|
| Url | https://urlxyz.com |
| Error description | Operation timed out after 5001 milliseconds with 0 bytes received |
Downtime verified from Paris, France and Bangalore, India
Downtime verified from Paris, France and Bangalore, India
urlxyz.com has recovered after 2m. full report: https://ohdear.app/monitors/83/checks/411
urlxyz.com seems down! Error: HTTP/500 Downtown verified from Paris, France and Frankfurt
Pushover has been successfully enabled. We'll notify you when something goes wrong.
urlxyz.com has recovered after 2m. full report: https://ohdear.app/monitors/83/checks/411
urlxyz.com seems down! Error: HTTP/500 Downtime verified from Paris, France and Frankfurt
ntfy has been successfully enabled. We'll notify you when something goes wrong.
urlxyz.com has recovered after 2m. full report: https:/ohdear.app/monitors/83/checks/411
urlxyz.com has recovered after 2m. full report: https:/ohdear.app/monitors/83/checks/411
Text messages for urlxyz.com have been successfully enabled. We'll notify you when something goes wrong.
$_TOKEN="your API token" $ curl -X GET "https://notifyservicexyz.com/api/alert/urlxyzcom" \ -H "Authorization: Bearer $_TOKEN" \ -H "Accept: application/json" \ -H "Content-Type: application/json"
urlxyz.com has recovered after 2m. full report: https://app.opsgenie.com/monitors/83/checks/411
urlxyz.com seems down! Error: HTTP/500 Downtown verified from Paris, France and Frankfurt
Opsgenie has been successfully enabled. We'll notify you when something goes wrong.
urlxyz.com has recovered after 2m. full report: https://pagerduty.com/monitors/83/checks/411
urlxyz.com seems down! Error: HTTP/500 Downtown verified from Paris, France and Frankfurt
PagerDuty has been successfully enabled within Oh Dear. Notifications are enabled.
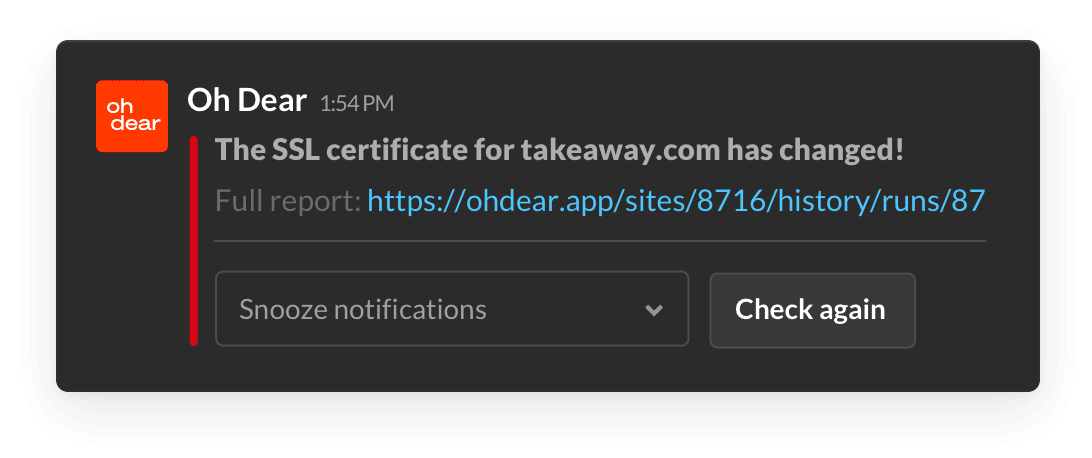
Choose how we let you know
Receive our notifications on your preferred platform. Via email, SMS, Slack, Discord, Opsgenie, PagerDuty, Microsoft Teams, Pushover, ntfy, webhooks,… we can notify you wherever your team is active.
Take notifications to the next level: only notify who needs notifying by assigning responsibilities to different team members.
Stop worrying, start monitoring
Start a no-strings-attached 10-day free trial. You're all set in less than a minute. (No credit card needed.)
Not convinced yet? Need help? Get in touch via [email protected].
Let’s get technical (if you’re into that)
You don’t need to be computer savvy to set up our tool. But if you are, we’re happy to explain exactly how it works and how you can customize Oh Dear to your specific needs.
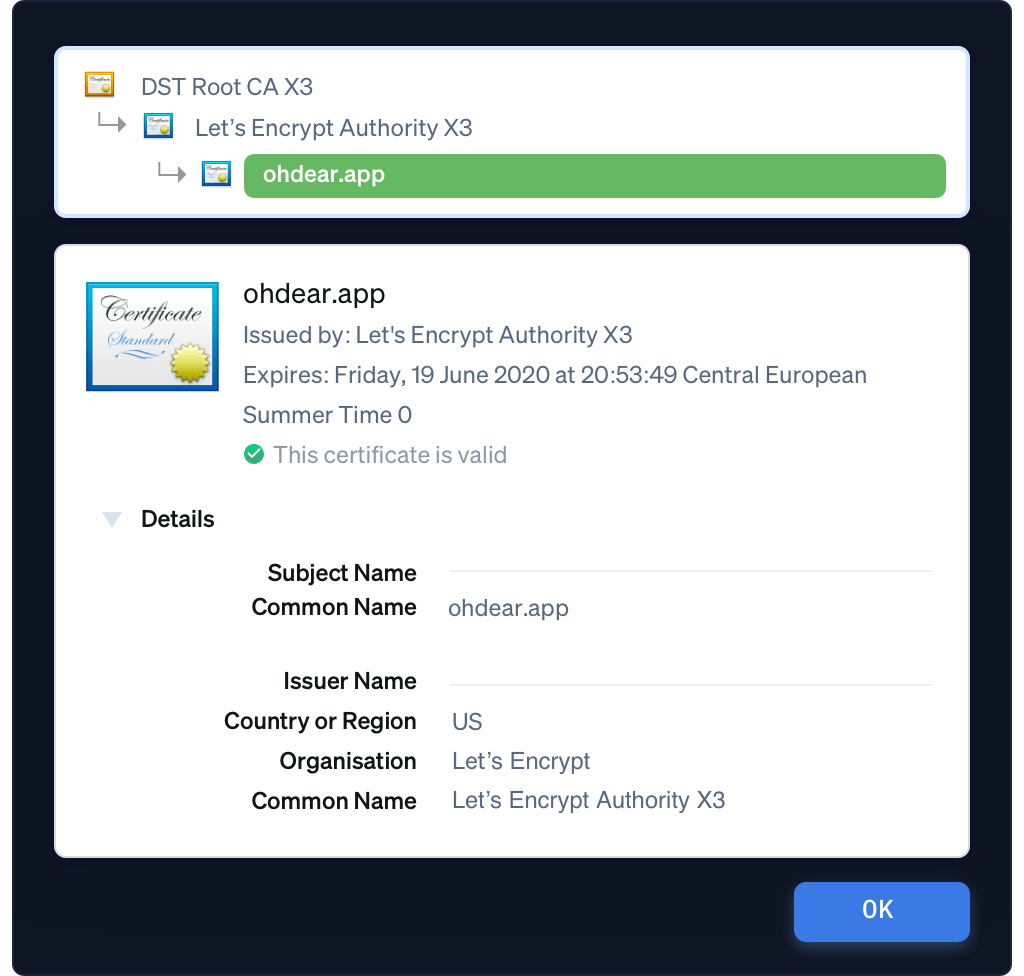
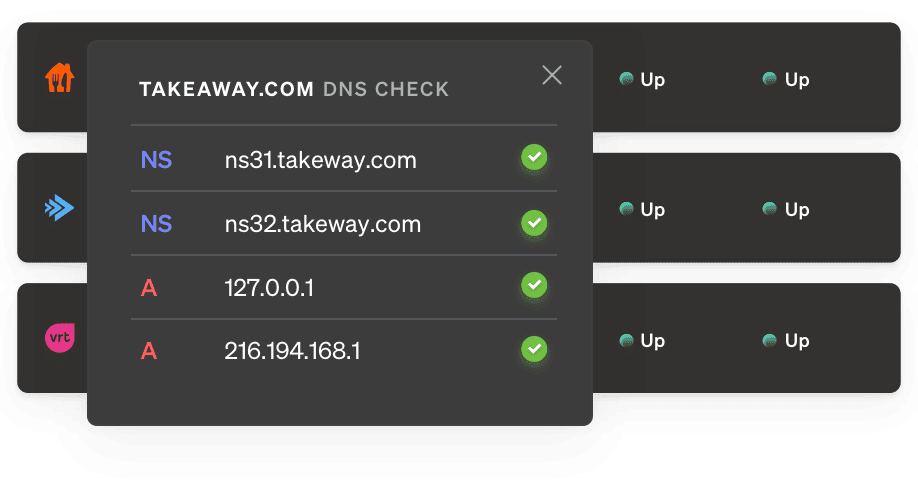
Certificate Chain Validation
A chain is only as strong as its weakest link. SSL certificates are the prime example.
We don't just monitor your domain certificate but will check every intermediate certificate too, up to the root certificate, to verify the chain of trust.
We look for SHA-1 certificates, revoked or distrusted root certificates, ... each of these can cause your site to be unavailable. And none of those changes are in your control, these decisions get made by the Certificate Authorities (CAs) or the browsers themselves, coordinated via the CAB Forum.
In a chain, every certificate could cause a problem for your website. We monitor each and every one of them.
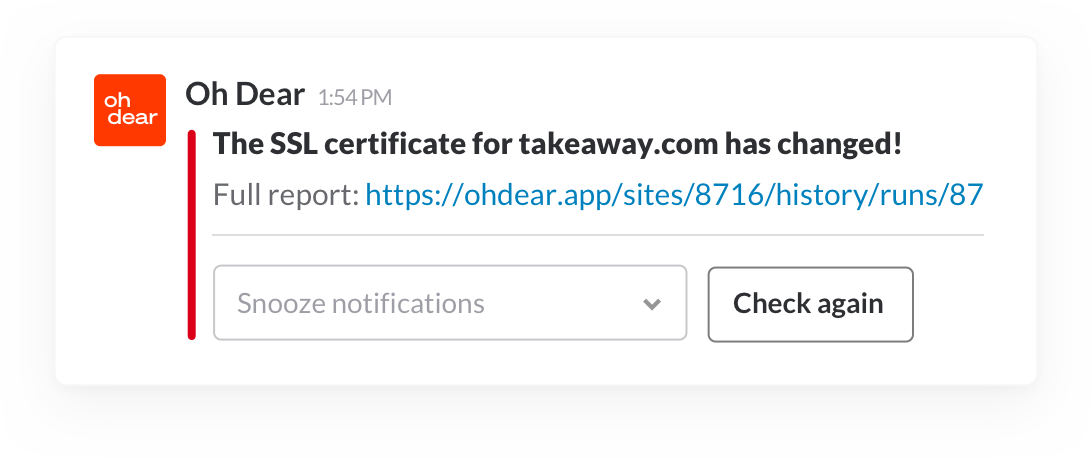
Certificate Change Detection
When a certificate is changed, we'll let you know straight away. We'll show a clear before/after comparison of the certificates we found, so you can verify that this change is both intentional and correct.
A changed certificate could be a renewal, but might also be a move to a new server (with a DNS change) or a domain hijack. We'll make sure you see each change!
Wait, there's even more
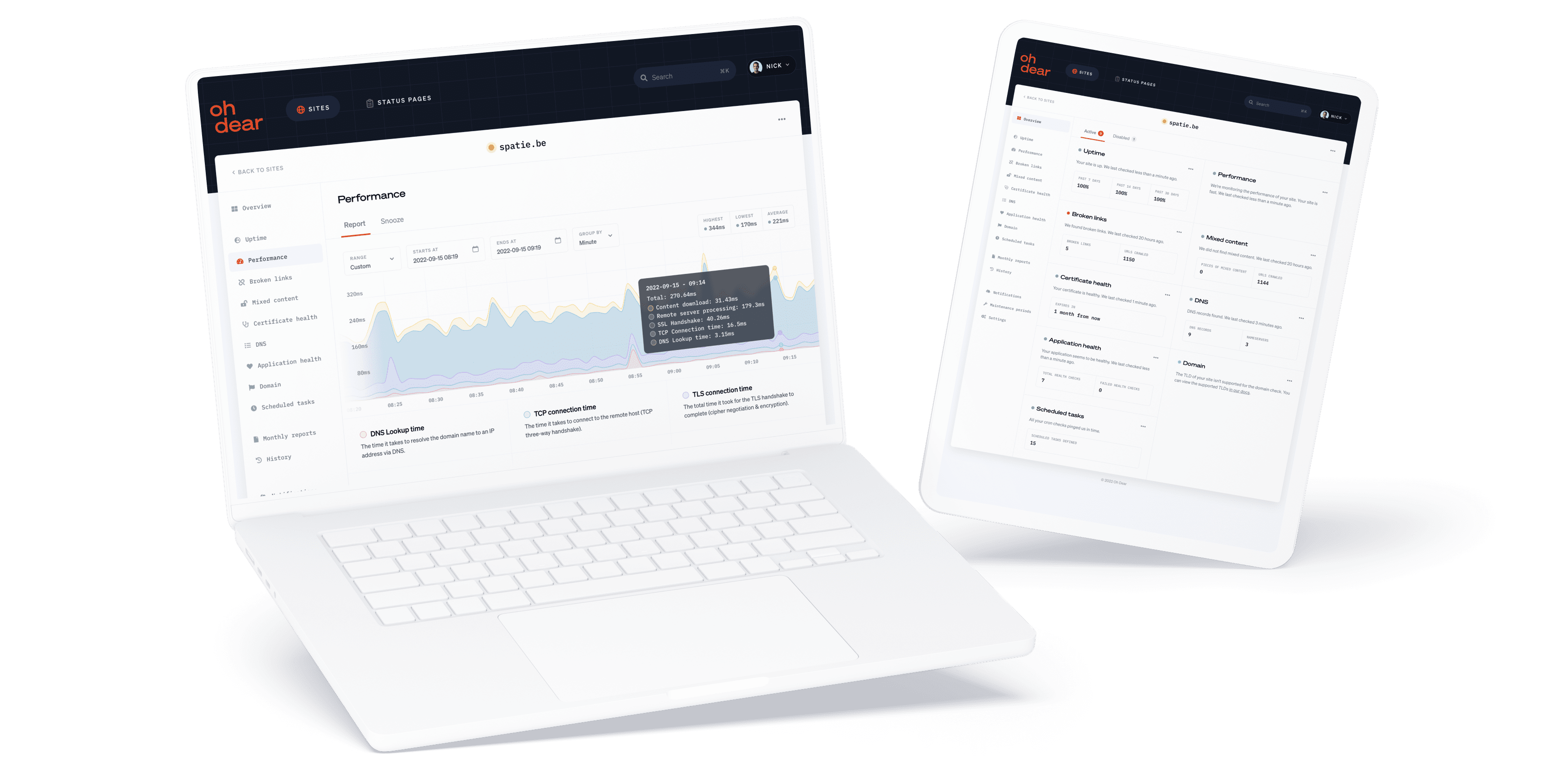
Performance monitoring
We provide highly detailed performance monitoring and insights. We'll notify you as soon as we detect your website is getting slow.
Fast and insightful notifications
Get notified instantly as soon as we detect an issue or an important change. Enable any channel you use, you're in full control.
Scheduled task monitoring
Your cron jobs (Linux) and scheduled tasks (Windows) are the heart of your data processing. We can monitor every single one of them.

Broken page & mixed content
We crawl and index your entire website, just like Google. As soon as we detect a broken link on your site we will let you know.
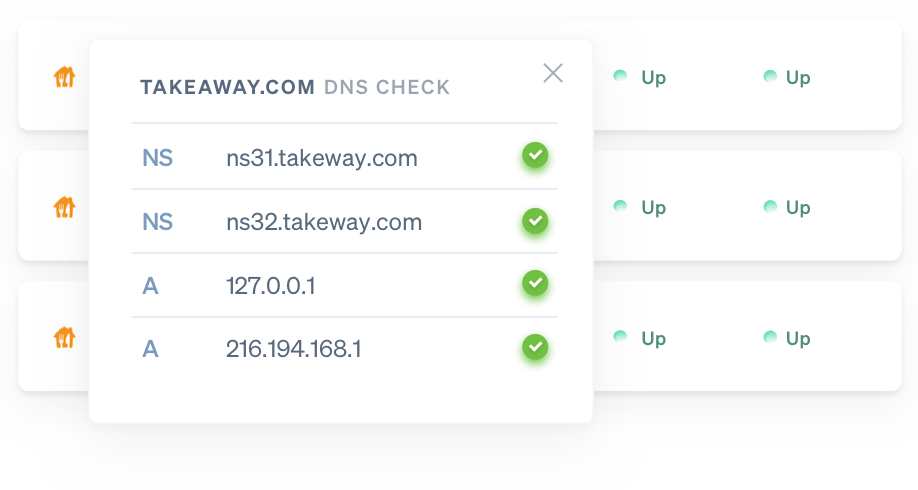
DNS record monitoring
Receive a notification whenever your DNS records are modified - intentionally or maliciously - so you can act and verify faster.
Application health monitoring
A lot can go wrong inside your app and server. Disk space may fill up, or the database may go down. We'll notify you when something is off.
Beautiful public status pages
In times of crisis, a public status page allows you to communicate to your clients. We'll host your status page so it's always available.
Website uptime monitoring
When your website goes down we'll let you know instantly. Now you can act before your or your client's brand reputation takes a hit.
Domain monitoring
We can check how long your domain is still registered. If your renewal date is close, we'll notify you. This will avoid you losing your domain.
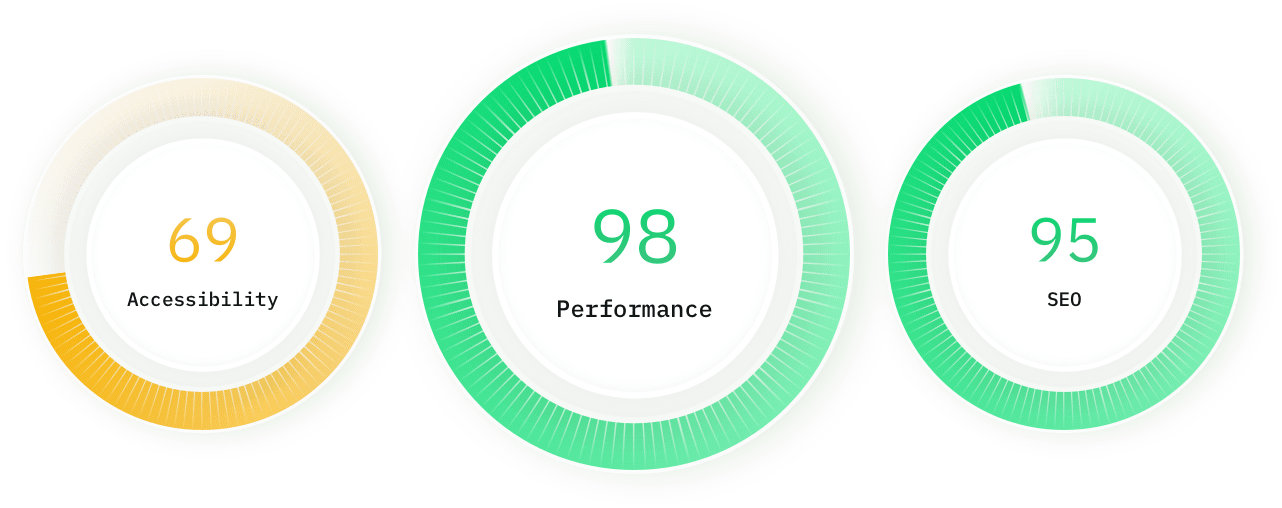

Lighthouse SEO monitoring
We track the speed & performance of your website over time. If we detect your website is suddenly slower, we'll let you know.
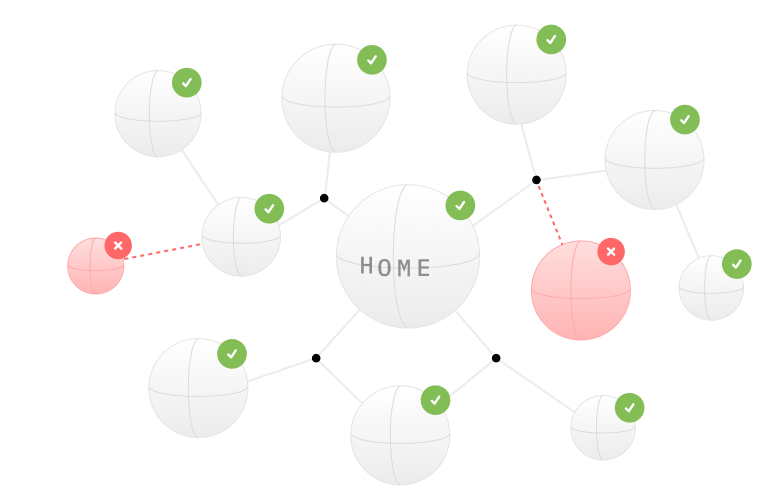
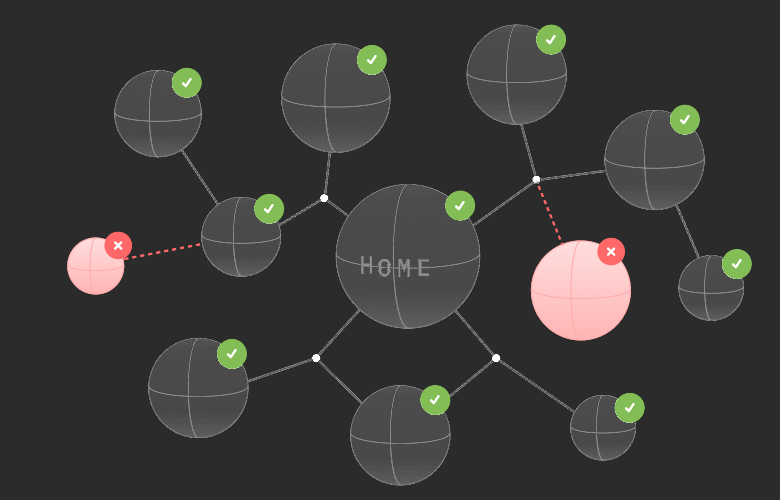
Sitemap monitoring
Elevate your SEO strategy and optimize your site. We analyse your sitemap health and check every URL for broken links.
Describe what you want to monitor
AI-powered monitoring
Use AI to verify anything you want on your websites and services with Oh Dear's AI-powered monitoring feature.
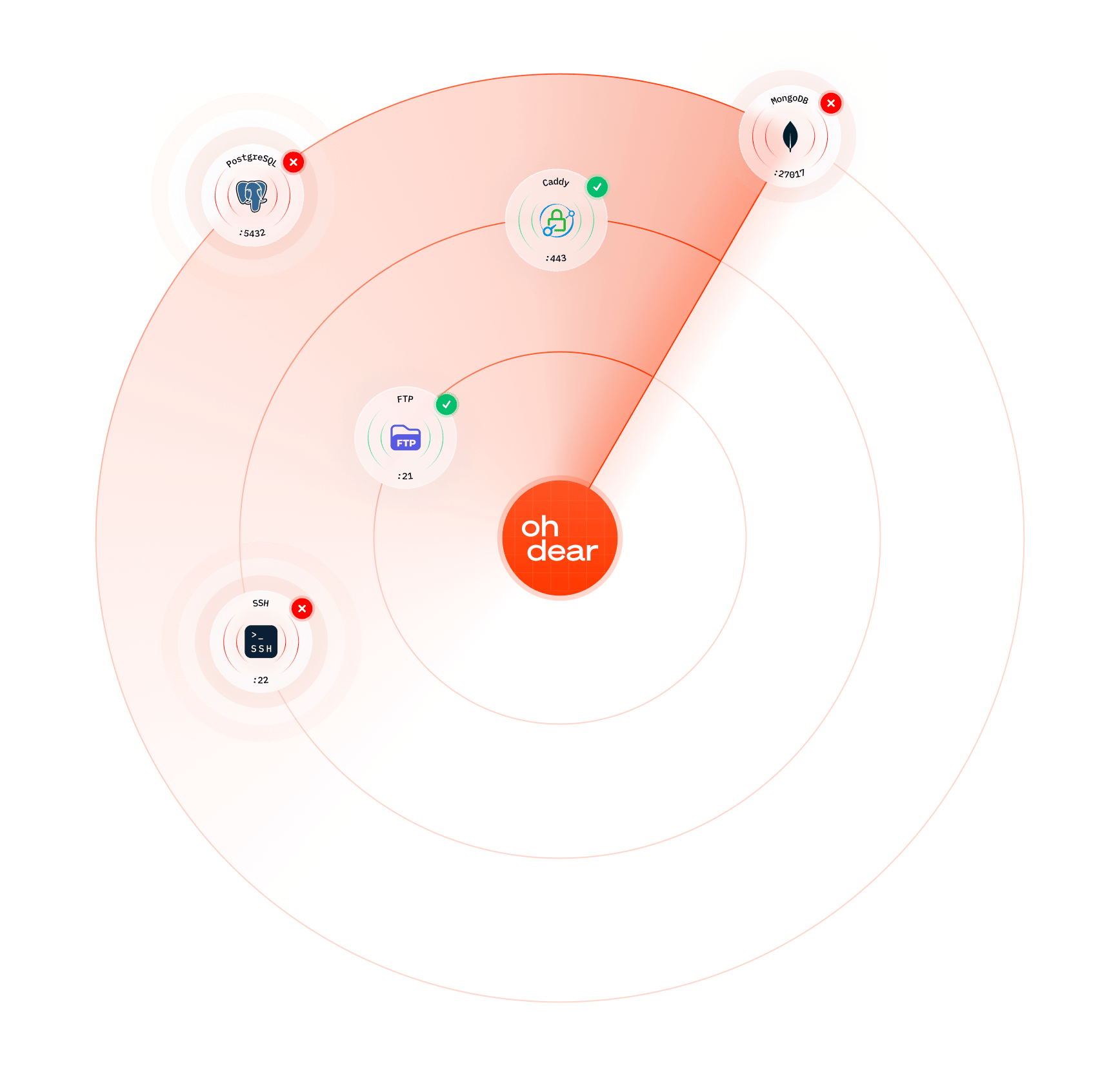
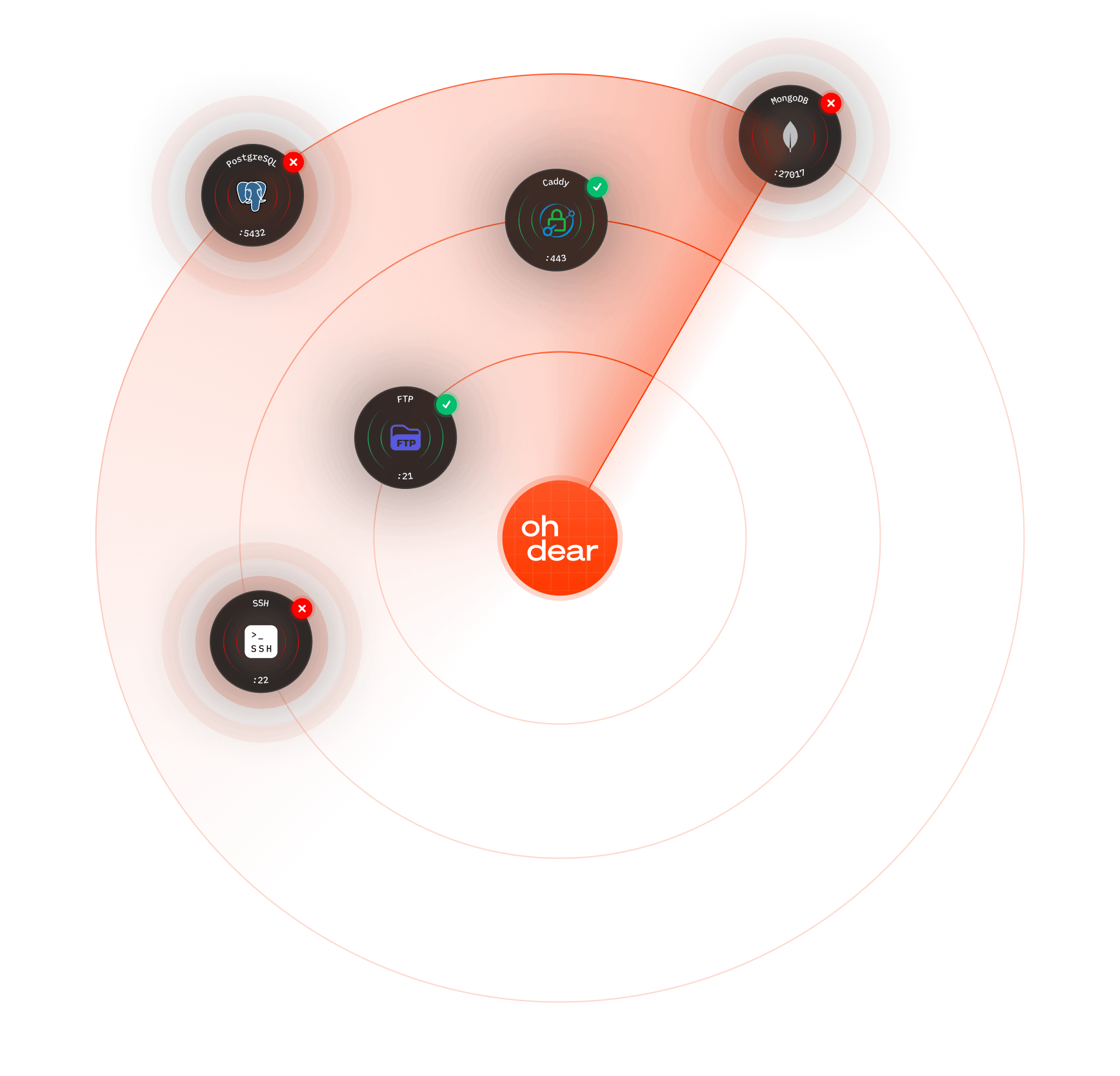
Port scanning monitoring
Port scanning monitoring keeps an eye on important ports that should either be open or closed. Get notified when a port changes state unexpectedly.
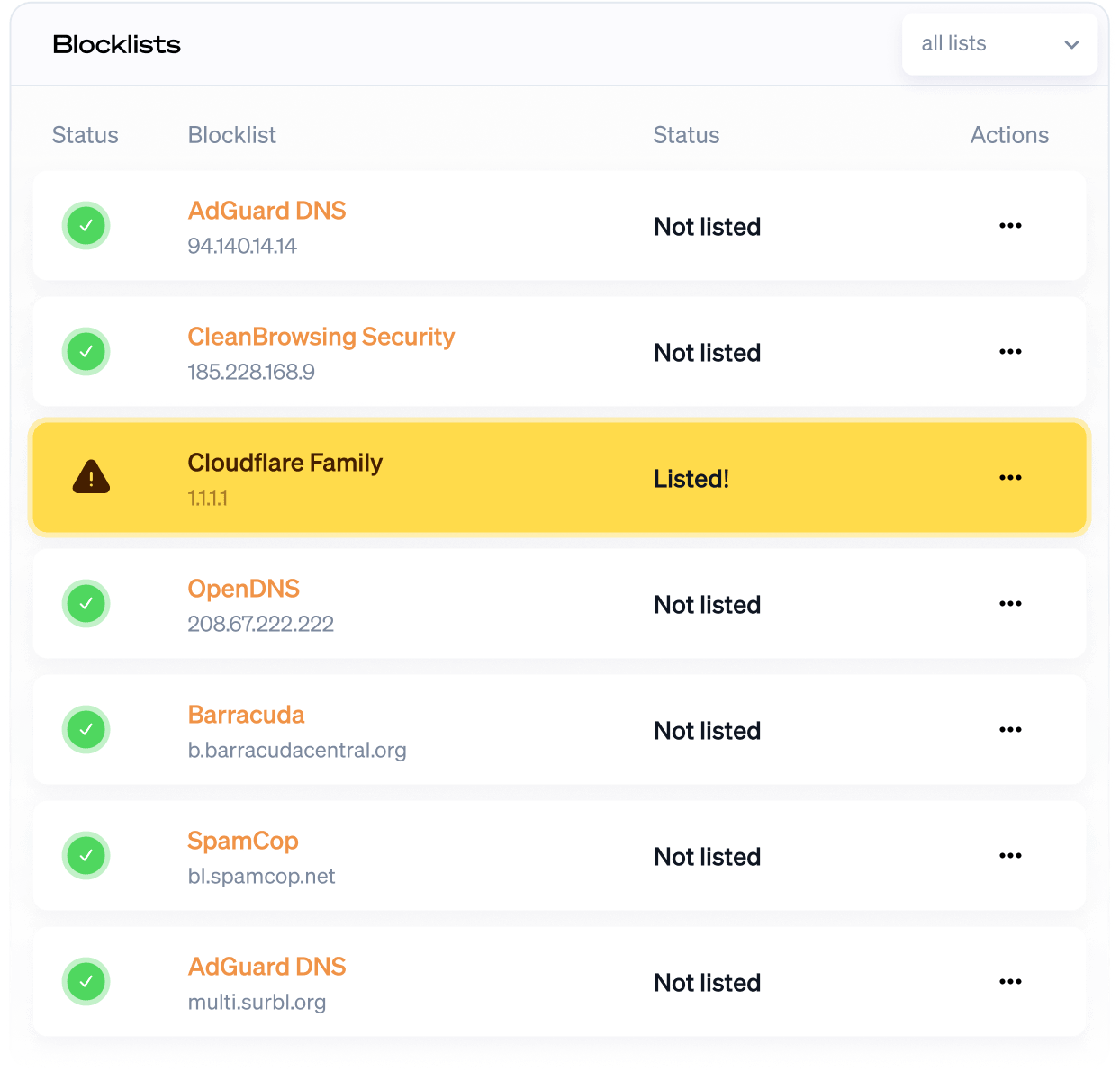
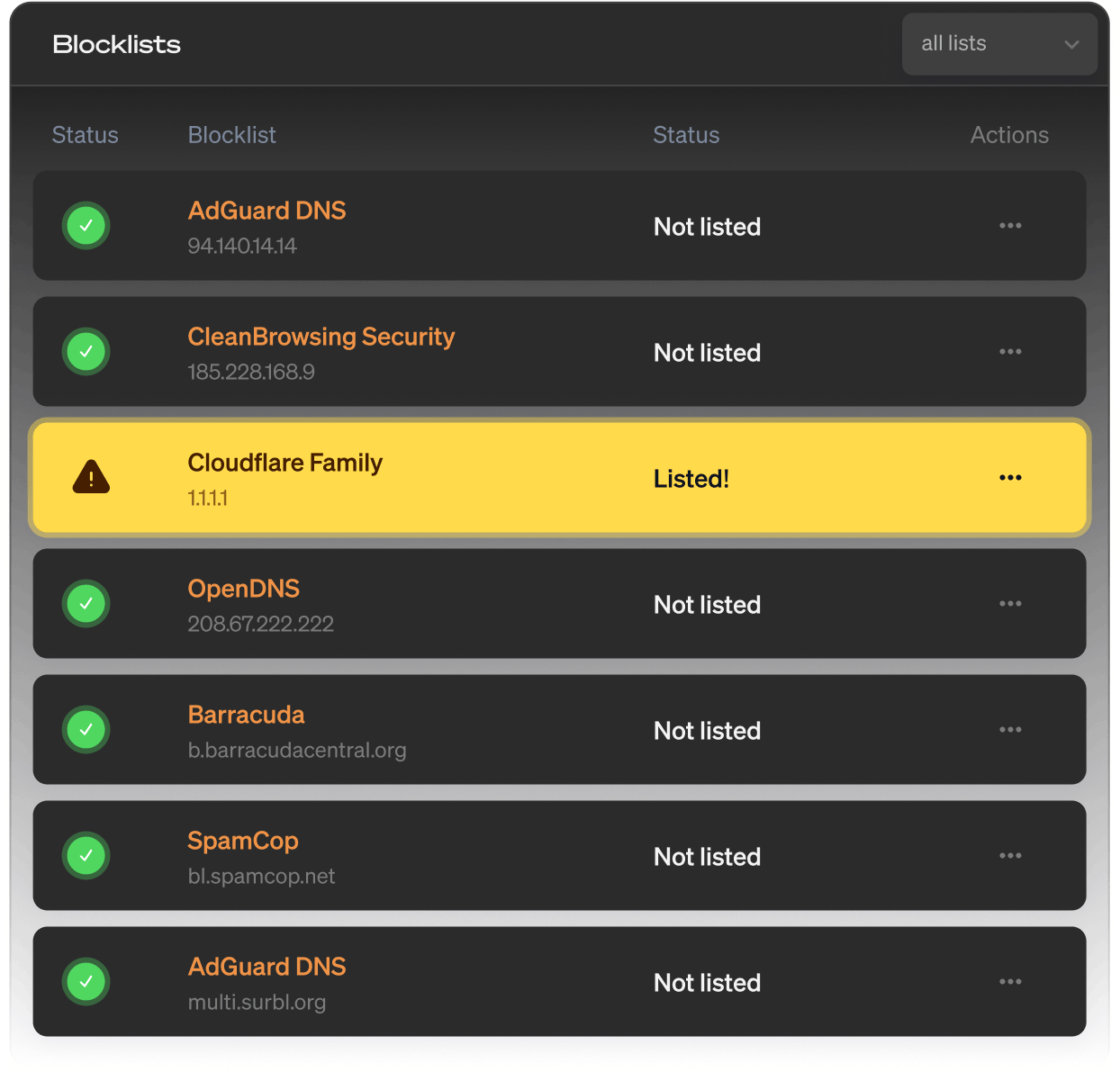
DNS blocklist monitoring
DNS blocklist monitoring helps you stay off spam and ad-block lists. Get notified when your DNS is blocked by a blacklist.
Single Sign-On (SSO)
Connect Oh Dear to your identity provider. Your team signs in with the credentials they already use.

Start monitoring instantly
Start a no-strings-attached 10-day free trial. You're all set in less than a minute. (No credit card needed.)
Not convinced yet? Need help? Get in touch via [email protected].