What are SSL/TLS certificates and why do I need them?
These days, every website is expected to be fast, reliable, and secure. The secure part is what SSL/TLS certificates handle. They're the reason your browser shows a padlock (and not a big red warning) when you visit a site.
Let's walk through what they are, why they matter, and what to keep in mind now that certificate lifetimes are getting dramatically shorter.
What is an SSL/TLS certificate?
SSL stands for Secure Sockets Layer. It's the original technology for setting up an encrypted connection between a browser and a server. SSL has since been replaced by TLS (Transport Layer Security), but the "SSL" name stuck, and most people still use the two terms interchangeably.
A site with a valid certificate serves traffic over https:// and shows a padlock in the address bar. That means the data going back and forth, passwords, payments, form submissions, is encrypted and tamper-resistant.
Why does a certificate matter?
Certificates aren't a "nice to have". Every modern website needs one, for several reasons:
- Encryption: sensitive data (passwords, payments, PII) is protected in transit
- Trust: visitors see the padlock and know the connection isn't being tampered with
- SEO: Google explicitly favors HTTPS sites in search rankings
- Compliance: GDPR, PCI-DSS, HIPAA, and most other frameworks expect encrypted transport
- No browser warnings: no full-page "Your connection is not private" pages driving visitors away
Are there different types?
Yes, a few, and they differ in what they verify:
- Domain Validation (DV): quick and automated. Proves you control the domain. Most Let's Encrypt certificates are DV.
- Organization Validation (OV): verifies your organization's legal existence on top of domain ownership.
- Extended Validation (EV): the most thorough level of validation. Once showed a green company name in the browser bar. Browsers have mostly dropped that UI, but EV still exists.
- Wildcard: covers
example.comand every subdomain (*.example.com) under a single certificate. - Multi-domain (SAN): covers multiple distinct domains in one certificate.
For most websites, DV is plenty.
Why certificate management is harder now
Getting a certificate installed is only the start. You also need to make sure it stays valid, and that's becoming meaningfully harder.
In April 2025, the CA/Browser Forum approved a plan to progressively shorten publicly trusted TLS certificate lifetimes, ending at 47 days by March 2029. That's a huge shift from the previous 398-day maximum, and the reduction will happen in several stages before 2029.
Shorter lifetimes are a net win for security: if a certificate is compromised, the exposure window shrinks dramatically. But they also mean renewing your certificates roughly eight times more often than before. At 47-day lifetimes, manual tracking is essentially impossible for anyone with more than a handful of domains.
What happens if a certificate expires?
Visitors get a full-page warning (Chrome's "Your connection is not private", Safari's "This Connection Is Not Private", etc.) and your site effectively disappears from the public web until the certificate is renewed.
That costs you:
- Traffic (visitors click away)
- Trust (the warning is alarming)
- Revenue (nobody's buying during the outage)
- SEO (Google logs the error on every crawl)
With lifetimes heading toward 47 days, the number of ways this can happen accidentally keeps climbing. Automating renewal is no longer optional. Monitoring renewals is just as important, because "automated" doesn't mean "definitely worked".
Seeing an invalid certificate alert while the site loads fine in your browser? That's usually a chain issue or SNI mismatch, not an expired cert.
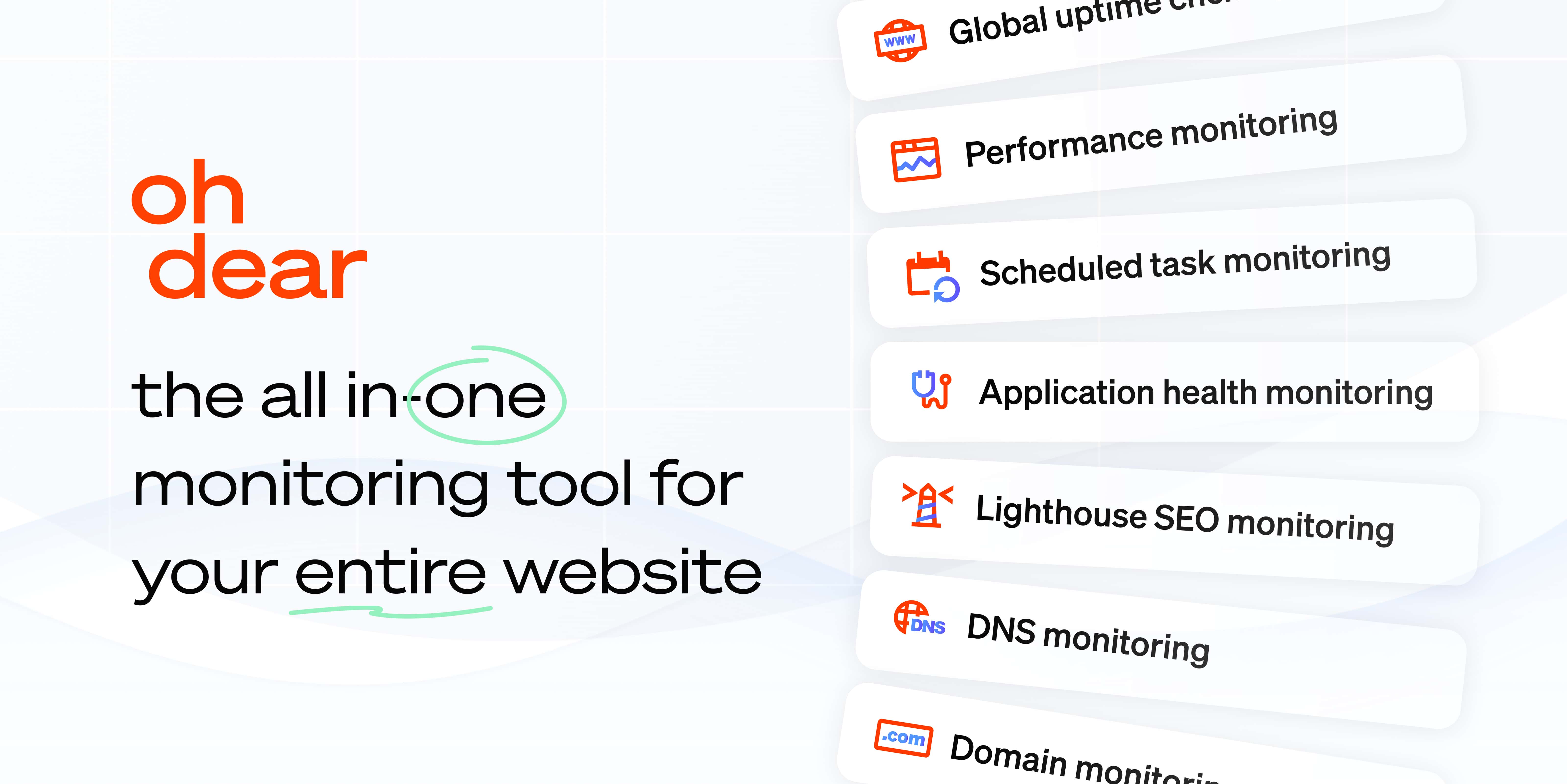
How Oh Dear helps
Oh Dear runs continuous certificate health checks against every monitor you add. For each check we verify:
- Whether the certificate is valid and trusted
- Whether the full certificate chain is present
- How close it is to expiration
- Whether the domain names in the certificate match the monitor URL
We don't renew certificates (we're not a CA, and getting into that business isn't our job). We tell you the moment something's off, so you can renew before it becomes a visible outage.
Custom expiration warnings
Every team works on a different cadence. Oh Dear lets you set the warning window per monitor, whether you want a heads-up 14 days before expiration or 30 days before (or both). With 47-day lifetimes becoming the norm, getting notified early matters more than it used to.
Alerts can go out over email, Slack, Microsoft Teams, Discord, Telegram, SMS, PagerDuty, Opsgenie, webhooks, and more.
Best practices for SSL/TLS certificate management
- Pick a reputable Certificate Authority. Let's Encrypt is free and great for most cases. DigiCert, GlobalSign, Sectigo are solid commercial options.
- Automate renewals. With lifetimes shrinking, manual renewal isn't sustainable. Use ACME (Let's Encrypt, ZeroSSL, Buypass) wherever you can.
- Redirect HTTP to HTTPS. All traffic, always.
- Enable HSTS. Tells browsers to only ever use HTTPS for your site, which protects against downgrade attacks.
- Monitor every certificate you serve. Automation fails. Monitoring catches the failures.
- Audit regularly. Check for mismatched domains, incomplete chains, and outdated TLS versions (1.0 and 1.1 should be off everywhere by now).
Wrapping up
Certificates have gone from "install and forget" to "renew constantly and watch closely". The good news: with the right automation and a monitor keeping an eye on things, you barely have to think about them.
Don't wait until a visitor tells you the site has a big scary warning. Start monitoring your certificates with Oh Dear, free for 30 days, no credit card needed.