Single Sign-On is now live in Oh Dear
Published on April 27, 2026 by Mattias Geniar
Single Sign-On is now generally available in Oh Dear, on every plan. Your team signs in with the credentials they already have, and you manage access from one place: your identity provider.
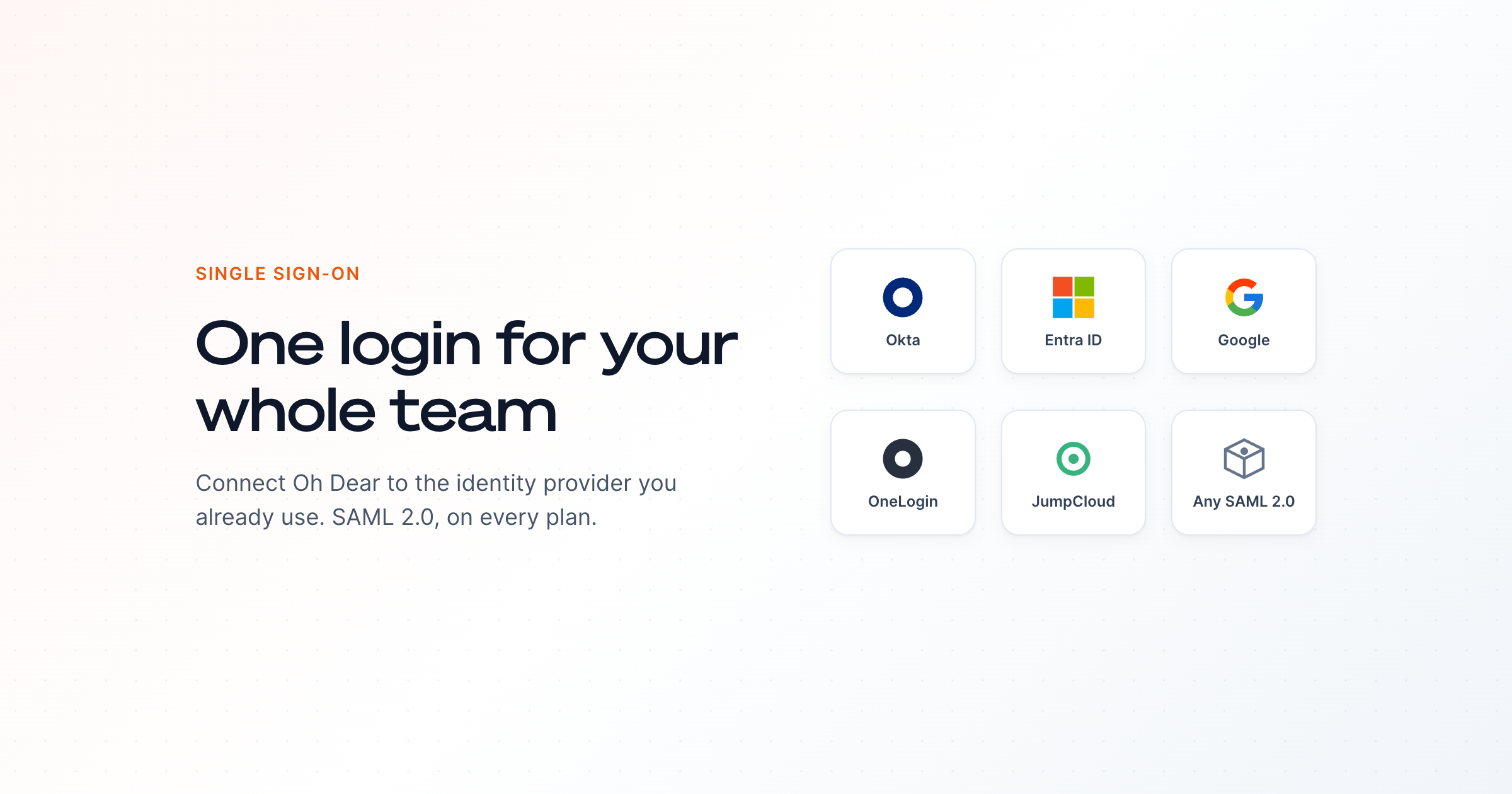
One login for your whole team #
When someone joins your team, you add them in your IdP and they have access. When someone leaves, you disable them in your IdP and access is gone. No shared logins, no forgotten accounts, no scrambling to revoke access across yet another tool.
That's the whole point of SSO, and it's now part of every Oh Dear team:
- New team members get access through your IdP
- Departing team members lose access automatically
- One set of credentials, one place to enforce policy
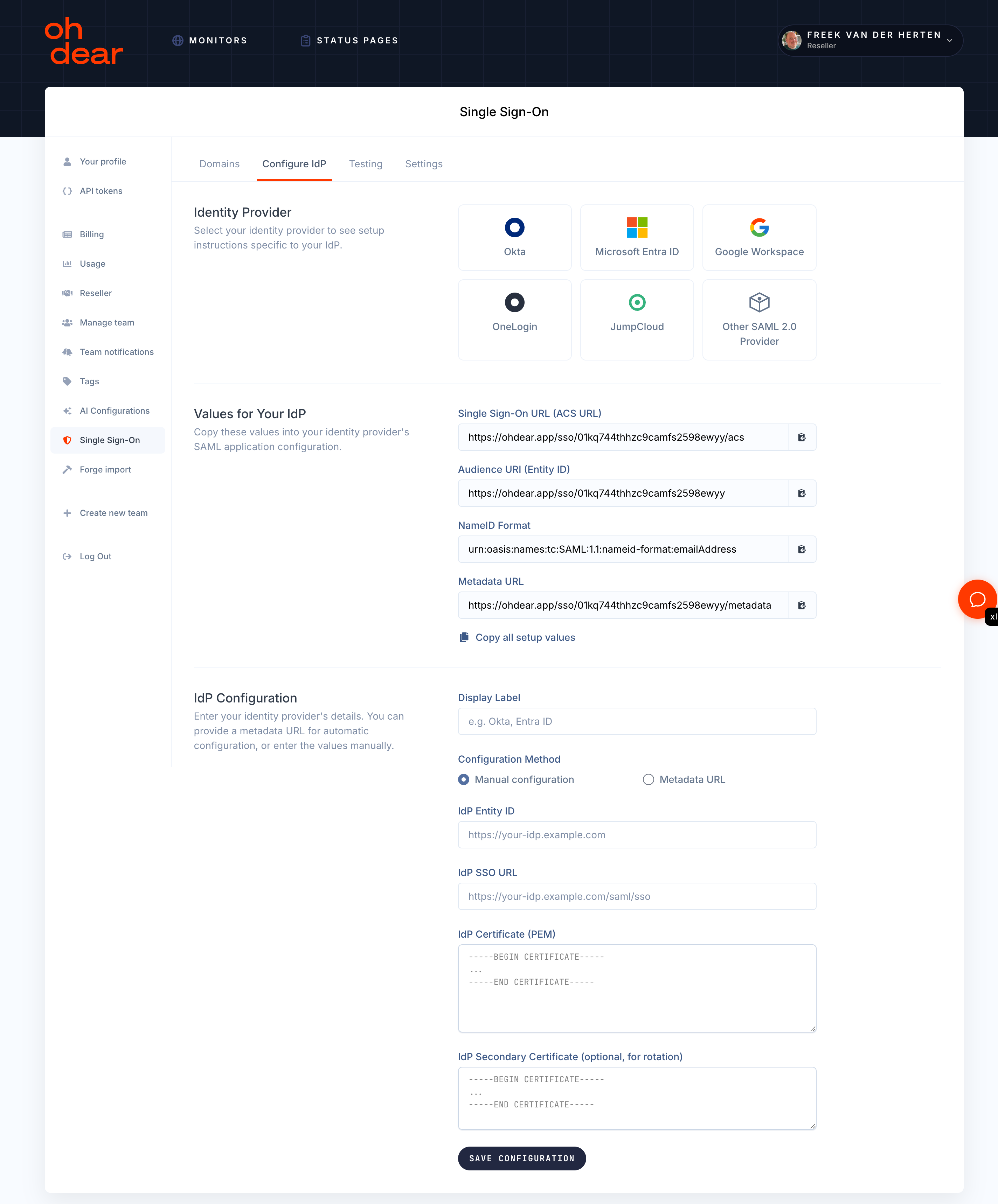
Guided setup for the IdPs you already use #
We built step-by-step setup flows for the providers most teams already have:
- Okta
- Microsoft Entra ID (formerly Azure AD)
- Google Workspace
- OneLogin
- JumpCloud
Pick yours from the list and Oh Dear walks you through the SAML configuration with the exact values you need to copy into your IdP. Most teams are done in under five minutes.
Using something else? Anything that speaks SAML 2.0 will work. Auth0, PingFederate, Keycloak, your in-house IdP, the lot. Pick "Other SAML 2.0 Provider", paste in the metadata URL or the certificate, and you're set.
Built for the way teams actually work #
A few things we cared about while building this:
- Email-first login. Your team enters their email on the normal login page. If their domain is configured for SSO, they're redirected to your IdP. If not, the password field appears. No separate URL to remember.
- Enforce SSO when you're ready. Flip a switch and password login is blocked for all non-owner team members. API tokens keep working, so your CI and automation don't break.
- Owner break-glass. Team owners always keep password access. If your IdP has a bad day, you can still get into Oh Dear. Every break-glass login is recorded for audit.
- DNS domain verification. Before SSO can be enabled, you prove ownership of your email domain via a DNS TXT record. No one can hijack your team's authentication by claiming a domain they don't own.
- One-time linking emails. Existing team members link their account to their IdP identity through a signed email link, not silent matching by email address.
If you're a CTO or operations lead, SSO isn't a nice-to-have. It's how you stay compliant, how you onboard and offboard people without forgetting a tool, and how you keep your auth surface area small. We kept it on every plan because security shouldn't sit behind an enterprise tier.
Try it #
Head to Team Settings > Single Sign-On in the Oh Dear app to verify your domain and connect your IdP. The SSO feature page has the full overview, and the SSO documentation has the step-by-step setup, provider-specific walkthroughs, and the answers to the questions you'll have along the way.
A more technical write-up on how we built this, the SAML choices, certificate rotation, and the security model, is coming next.